Navigating Canada’s Privacy Landscape
Understanding Your Compliance Obligations Privacy is a rising concern for organizations across sectors, as well as a renewed focus for legislators and regulators. Canada’s privacy legal landscape is complex, with federal and provincial laws, sector specific laws, and common law forming a network of protection for individual privacy rights. It is important for organizations to…

How Effective Is Your Privacy Program?
Developing a Mature Privacy Program Most organizational leaders understand privacy as a priority. They know that their organization needs a legally compliant privacy policy and a qualified privacy officer, and that new technological tools should be evaluated from the perspective of privacy. Once these basics are in place, however, they often have a harder time…

Getting Your Organization on Board with Privacy
Establishing a culture of privacy Ten years ago, privacy was a new conversation for many organizations. Today, the leaders of most large organizations are talking about it. Boards’ and executives’ top concerns are: Meeting increased regulatory requirements Preventing or responding to data breaches Navigating the pitfalls and prizes of data analytics In the age of…

What Do I Need to Know About US and EU Privacy Legislation?
Data’s fluid and global nature creates a complicated network of international legal obligations.

Series: Bringing Privacy Regulation into an AI World
Over the past decade, privacy has become an increasing concern for the public as data analytics have expanded exponentially in scope. Big data has become a part of our everyday lives in ways that most people are not fully aware of and don’t understand.

Moving from Access Control to Use Control
Bringing Privacy Regulation into an AI World, Part 5 I would like to outline a new concept of use control: a way of designing AI systems so that personal data can be used only for specified purposes.

Is AI Compatible with Privacy Principles?
Bringing Privacy Regulation into an AI World, Part 2 Many experts on privacy and artificial intelligence (AI) have questioned whether AI technologies such as machine learning, predictive analytics, and deep learning are compatible with basic privacy principles.

Do We Need to Legislate AI?
Bringing Privacy Regulation into an AI World, Part 1 In recent years, artificial intelligence (AI) and big data have subtly changed many aspects of our daily lives in ways that we may not yet fully understand. As the Office of the Privacy Commissioner (OPC) of Canada states, “AI has great potential in improving public and…

Why Canadian Privacy Enforcement Needs Teeth
Bringing Privacy Regulation into an AI World, Part 7 This seven-part series explores, from a Canadian perspective, options for effective privacy regulation in an AI context. In this series on bringing privacy regulation up to date for a world of big data and AI, I have discussed the need for revised legislation, the continued relevance…

Implementing Use Control: The Next Generation of Data Protection
Bringing Privacy Regulation into an AI World, Part 6 In my last few posts, I have discussed the crucial difference between access control and use control as tools for protecting privacy in an AI context. Access control has been highly effective in managing security threats – so much so, in fact, that external hacks are…

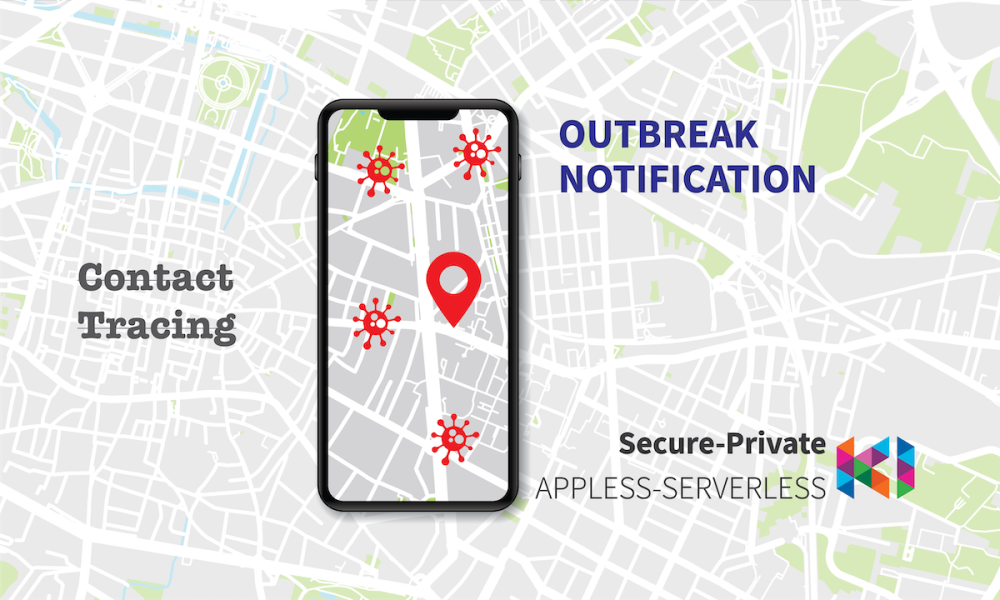
A 3D Test for Evaluating COVID Alert: Canada’s Official Coronavirus App
Great news – Canada has just released its free COVID-19 exposure notification app [1], COVID Alert. Several questions now arise: Is it private and secure? Will it be widely adopted? And how effective will it be at slowing the spread of the virus? We have evaluated the COVID alert app against three dimensions: Concept, Implementation,…

Outbreak Notification App Design
From Contact Tracing to Outbreak Notification Call for Participation As countries assess how best to respond to the COVID-19 pandemic, many have introduced smartphone apps to help identify which users have been infected. These apps vary from country to country. Some are mandatory for citizens to use, such as apps released by the governments of…