Canada’s Security Agency Issues:Top 10 Actions to Take to Eliminate Cyber Threats
In this series of posts, we review recommendations for workplace cyber security published by the Communications Security Establishment Canada. Today, we offer commentary on CSEC’s Top 10 recommendations for strengthening cyber security. The Communications Security Establishment Canada’s (CSEC) Top 10 IT Security Actions bulletin offers ten recommendations that promise to eliminate the vast majority of cyber threats…

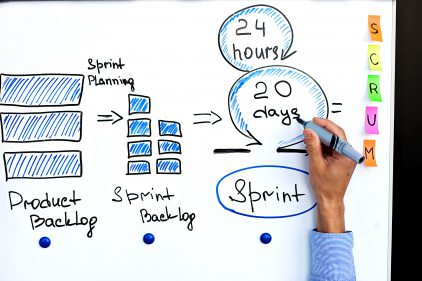
Agile Privacy for Modern Software Development
With the increasing popularity of agile IT, privacy officers responsible for assessing new software programs are finding it difficult to keep track of changes and ensure that proper checks are in place. We propose an agile approach to privacy assessment that can reduce confusion, increase compliance, and improve relationships between privacy and IT. Privacy Impact…

The Best Encryption ceases to work upon the first authorized access
Has encryption protect google and yahoo against NSA snooping, simply not. Was the NSA protected against data extract by an ‘authorized’ user who threatened the nations security? not really. Hence we say that best encryption ceases to work upon the first authorized access.

Governance Analysis Method – PhD Thesis Waël Hassan
Governance Analysis is a logic-based, computer assisted framework for validating legal compliance of enterprise governance models. This framework is intended to help check whether governance systems are consistent with the law. My approach to Governance Analysis includes legal and enterprise models, a governance analysis method (GAM), a governance analysis language (GAL), and an implemented governance…

An Enterprise Legal Reference Model
We have developed an enterprise reference model used to conceptualize enterprise elements. The model suggests three planes: Subject and role-grouping plane: In this plane, the subjects are grouped into roles. Roles reflect subject access rights into the processes and activities of the middle plane. Process and activity plane: Here, processes are organized in a hierarchy…